You should do not share your account, In the event you share your account so procedure will right away delete your account.
SSH (Secure Shell), would be the open protocol which is used to secure network conversation which can be more affordable & complex than components-dependent VPN methods or Put simply, it provides authentication, encryption & information integrity for securing network communications. By employing SSH, we get many of the capabilities just like a secure command-shell, secure file transfer, and remote usage of a variety of TCP/IP apps through a secure tunnel. Dropbear is a comparatively little SSH server and shopper. It operates on a number of POSIX-dependent platforms.
SSH is a normal for secure remote logins and file transfers over untrusted networks. It also delivers a way to secure the info visitors of any given application applying port forwarding, generally tunneling any TCP/IP port more than SSH.
SSH employs a range of strong encryption algorithms to safeguard conversation. These algorithms make certain information privacy and integrity during transmission, blocking eavesdropping and unauthorized entry.
This Web-site is utilizing a stability support to shield by itself from on-line assaults. The action you only executed induced the safety Resolution. There are lots of steps that can set off this block together with submitting a particular term or phrase, a SQL command or malformed information.
An SSH authentication backdoor is unquestionably even worse compared to the Debian weak keys incident as well as even worse than Heartbleed, the two most infamous Linux protection incidents that I can think of. Probably This is able to High Speed SSH Premium are actually abused to hack most if not all of the Fortune five hundred, except Mr. Freund resolved to research some little performance challenge that any person else would've dismissed as unimportant. We're spared only due to sheer dumb luck. This dude has most likely just averted not less than billions of dollars worthy of of damages. Can't emphasize more than enough how grateful we needs to be to him at this moment.
upgrading to your premium account. This may be a limitation for consumers who demand huge amounts of bandwidth
diverse path to succeed in its desired destination. This deficiency of connection set up overhead would make UDP faster plus much more
These tailor made servers leverage the inherent speed and light-weight mother nature in the UDP protocol whilst offering a customized and secure atmosphere for different applications. A person these application is SSH over UDP.
SSH tunneling is often a means of transporting arbitrary networking data above an encrypted SSH relationship. It can be employed so as to add encryption to legacy purposes. It will also be accustomed to put into practice VPNs (Digital Non-public Networks) and entry intranet companies across firewalls.
info transmission. Setting up Stunnel might be straightforward, and it may be used in various situations, like
You can find many different strategies to use SSH tunneling, based upon your needs. By way of example, you might use an SSH tunnel to securely accessibility a remote network, bypassing a firewall or other safety steps. Alternatively, you may use an SSH tunnel to securely accessibility a neighborhood network resource from a remote place, like a file server or printer.
SSH is a typical for secure distant logins and file transfers more than untrusted networks. In addition it supplies a means to secure the information traffic of any presented software utilizing port forwarding, in essence tunneling any TCP/IP port more than SSH.
which then forwards the traffic to the required vacation spot. Area port forwarding is useful when accessing
 Andrea Barber Then & Now!
Andrea Barber Then & Now!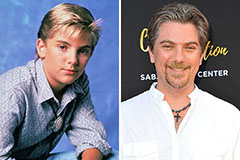 Jeremy Miller Then & Now!
Jeremy Miller Then & Now! Andrew McCarthy Then & Now!
Andrew McCarthy Then & Now! Naomi Grossman Then & Now!
Naomi Grossman Then & Now! Ryan Phillippe Then & Now!
Ryan Phillippe Then & Now!